October is almost done, so it’s time for another update! The supply chains are clearly haunted, so this one has a spooky theme.

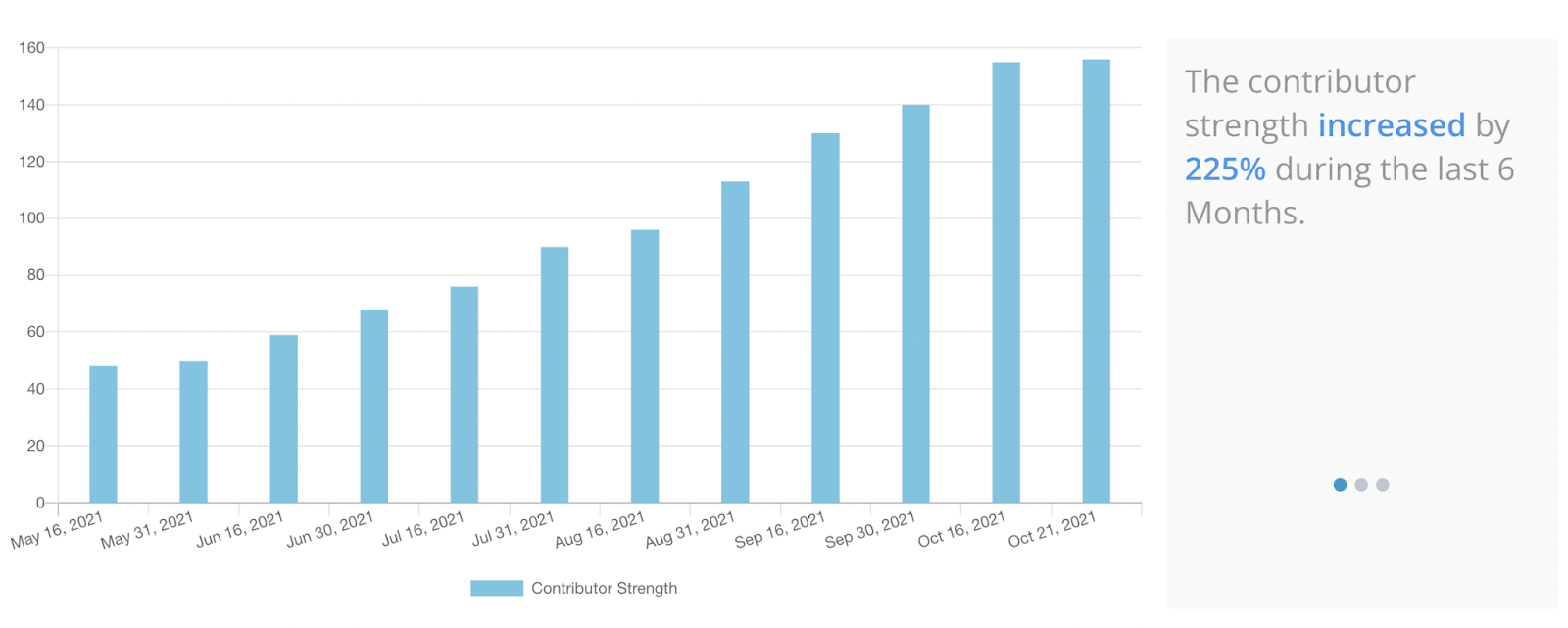
The community is still growing quickly, and the fancy new “Contributor Strength” dashboard reflects it!
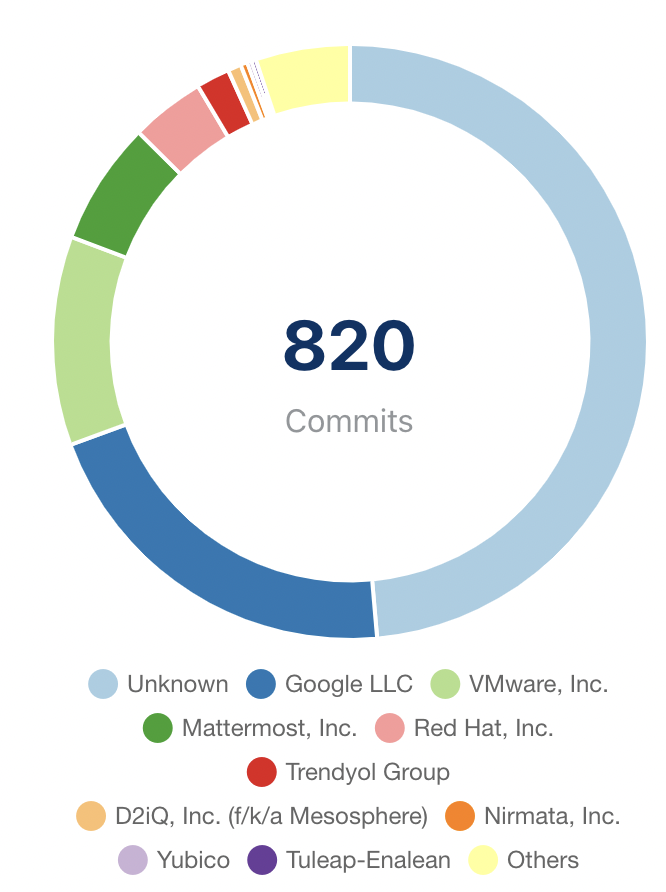
In other numbers, we’re at 820 commits from 85 committers, and our slack channel has reached 710 members! Keep the PRs coming everyone!
The Sigstore talk at Kubecon went very well, and the Sigstore booth was a huge success! We had over 300 people attend the virtual booth, and countless people come to the in person one with questions and support!
Cosign
The next release (v1.3.0) of cosign is nearing, with lots of changes and refactoring under the hood. We finally added support for standard POSIX flags ( —-hello-world!), and cleaned up our libraries considerably. The cosigned helm chart has been released in the CNCF Artifact Hub, and we spent some time cleaning up our own repo hygiene using the OpenSSF’s Scorecard project.
The most exciting new feature (in my opinion) is the support for validating Cue and Rego policies against In-Toto Attestations. You can see a demo of Cue here. Huge thanks to developerguy-ba, erkanzileli, and Dentrax for getting this in!
Rekor
The last piece of work in Rekor before declaring GA is temporal sharding of the log, which Lily Sturman has been driving. The log is close to 800k entries, including some important ones, like the provenance information generated during builds of the Distroless container images used to meet SLSA2. See the full blog post from Priya Wadhwa showing how to look these up and verify them here.
Sigstore
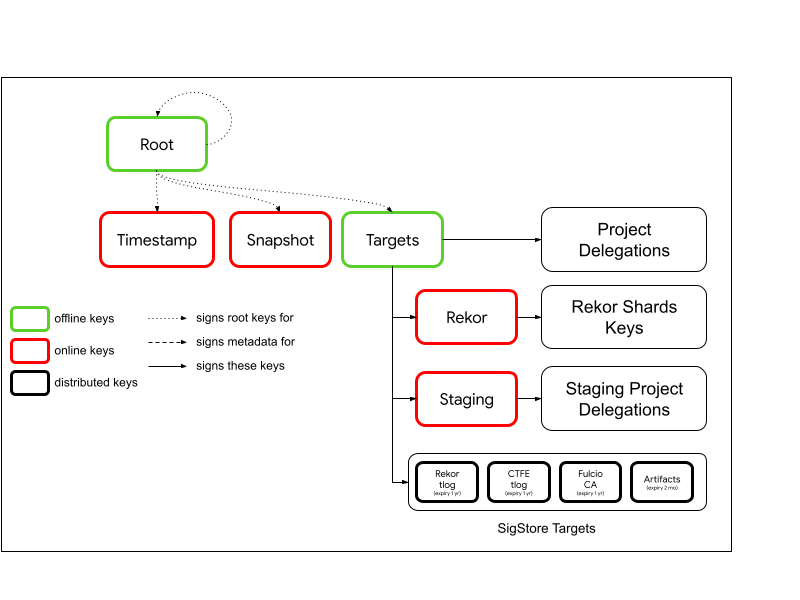
The Sigstore TUF Root V2 has now been signed, thanks to Asra Ali’s hard work! This root contains delegations for Rekor, Fulcio, and the ability to add more federation delegations for other open source projects and communities! In the words of Trishank Karthik Kuppusamy, this is “A Big Deal”:
Fulcio
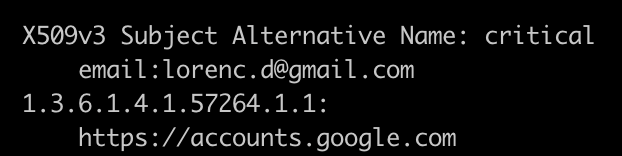
October has been a big month for Fulcio, or free Code Signing CA! Mark Bestavros landed support for AWS CloudHSMs, we have full support for GitHub Actions OIDC tokens, and Bob Callaway finished up a long-standing task around fully propagating the OIDC Issuer URL used for a specific challenge all the way into the final certificates (which live forever in transparency logs).
This means that in addition to an email address or machine account, you can also find the actual OIDC endpoint that Sigstore used to validate the identity against in the x509 certificate. For example, we can see that my email address was validated using accounts.google.com:
Community
We’ve also seen a huge increase in activity outside of the core Sigstore organization, with more and more projects adding support for supply chain transparency. The Syft project from Anchore is working on direct signature and attestation support for SBOMs using cosign. Quay 3.6 now supports cosign signatures, and Kyverno 1.5 provides native support for In-Toto Attestations. Keep these integrations coming, we love to see them!
